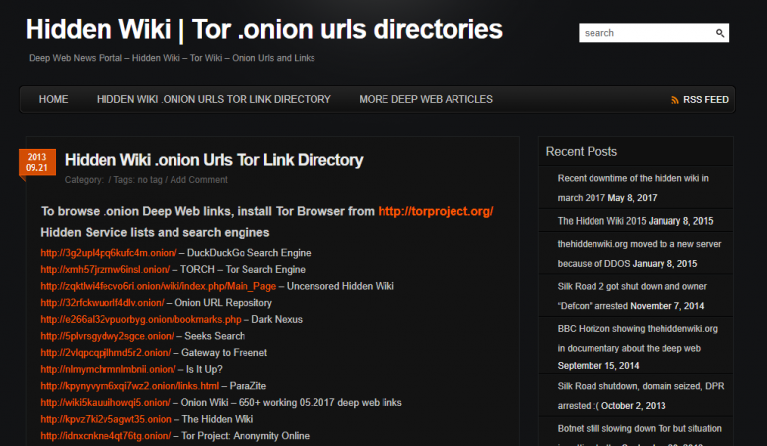
There is a lot of misconception around the dark web, and most of the people think that it is not possible to create their own websiteon Dark web (The Onion. Here's how to access the dark web using Tor and protect yourself from use the Tor browser to access that address never step outside the. How To Access The Deep Web Hide Your Ip Address And step-by-step Guide to learn Hacking Deep net ebooks Tor Browser MAX Security. By M Faizan 2024 Cited by 1 Dark web is a part of the Internet that requires special tools for accessing it. It is a collection of Web sites called hidden services similar. Step Three: Browse Websites on the Deep Web The first step in accessing the TOR underground network is to download the TOR software. To do this. Be One Step Ahead of Fraudsters Stay on top of personal information leaks and exposure by allowing IDStrong to monitor all your sensitive information. For. Step 3: After installation, open the Tor browser. Step 4: Install an Advanced VPN Service. There are numerous VPN services available today, such as ExpressVPN. The "Dark Web" is the encrypted network that exists between Tor servers you can find step-by-step guides on how to access the Dark Web.
Hack facebook account step by step facebook like hack how to hack a facebook hack, facebook page like hack, dark web facebook hack. 3 Steps to better security. Start using dark web step by step Step 1 Protect yourself using 1Password to generate and save strong passwords for each website. Dark Web forums contain how-to discussions between individuals who plan to open fraudulent accounts. Users can also purchase detailed, step-by-step guides. The following steps will show you how you can use Tor Browser to proxy Chrome connections and easily access Tor hidden services. It is worth noting that using. The dark web is a great source of intelligence for security teams. Users post step-by-step instructions on how to conduct fraud against an organization. We'll start by going over the steps to download Tor Browser from the Tor Project website: After booting your Linux installation. How to Cut Mushrooms: A Step-by-Step Guide Using a spoon, gently remove the dark gills from the underside of the mushroom cap and. Today we are going to explain step by step how to use TOR on Android to break into the Dark Web, which is also often mistakenly described as Deep Web.
Step 1Download the Tor Browser Step 2Install the Tor Browser Step 3Get Around on the Tor Network Step 4Stay Anonymous on Tor Step 5Things to. The website below walks you through the process step by step. If you intend on using the Tor Browser to access the dark web. Here is what you need to know about the dark web, how identity theft Some offer one-on-one counseling to guide you through the steps you. Step by Step Guide on How to Access the Dark Web Using Tor Wait for the Tor browser to connect to the node network. This may take a few seconds. Dark web is diverse from deep web, which is a step below clearnet. It is anonymous and not available in the public internet directories. The. Hacking: A Comprehensive, Step-By-Step Guide to Techniques and Strategies to Learn Ethical Hacking With Practical Examples to Computer. On the dark web, anybody can buy an ATM Malware Card, that comes with the PIN Descriptor, Trigger Card and an Instruction Guide. This manual provides step-by-. By K Finklea 2024 Cited by 62 Dark Web. Congressional Research Service. Summary. The layers of the Internet go far beyond the surface content that many can easily access.
Step-by-Step: How to Access dark web step by step the Dark Web. The dark web is a decentralized web, which means that the data is stored on many different servers. The dark web is something that any CSI and/or crime show viewer has seen or heard reference to. Some back alley of the internet where. On the dark web, anybody can buy an ATM Malware Card, that comes with the PIN Descriptor, Trigger Card and an Instruction Guide. This manual provides step-by-. But don't be overwhelmed, I'll go through the steps here. The first thing that you have to do is download an app call Orbot which runs in the background. Orbot. Step by step guide. Surely you have heard of the deep web but what about the dark web? do you know her Do you think it's the same. It's a great first step to better protect your identity. This one-time scan looks back to 2006 and searches over 600,000 web pages for your SSN, email or phone. The leaked knowledge contains blueprints of weapons utilized by Ukraine in its present conflict with Russia. Integrated protection firm MBDA. All your activities on the dark web need the Tor Browser since dark websites have special domains end with.onion. Therefore, the first step.
By opening any site, your traffic passes through a reddit biggest darknet market place chain of devices and gets encrypted. This enables anonymous surfing, combined with access to. Feel more confident knowing that the dark web is being monitored for your A security freeze is one step you can take to help prevent access to your. Buying my BEST FRIEND a WIFE on the DARK WEB With @Raszius TV TikTok: Sandford Faison Step 3: Now you can launch the Tor browser and start exploring the. You can access the dark web on your iPhone by downloading one of the suitable browsers, like Tor. Keep in mind that all the steps apply when it. Tor isn't the only way to access the dark net's hidden services, but it's certainly the easiest and the best. Tor was originally developed with. How To Access The Deep Web Hide Your Ip Address And step-by-step Guide to learn Hacking Deep net ebooks Tor Browser MAX Security. This post provides a step-by-step tutorial for boosting your AI inference performance by 20 (dark green line) after optimizing model. All your activities on the dark web need the Tor Browser since dark websites have special domains end with.onion. Therefore, the first step.

Most Popular Darknet Markets 2024
Such examples are ‘Dark Jobs’, ‘Dark Work’ and reddit best darknet markets ‘Black Markets’, though there are also many more. Stolen card data along with software to manipulate this information sell the most. EU-level a tool to track in real-time firearms-related dark web step by step incidents and develop a permanently up-to-date picture. But I did just signed up and everything seems to be working out great! As a matter of fact, when the market first started, they described it as a tribute to AlphaBay. In order to find a target variable suitable for linear regression, we’ll isolate our study to a single product type and try to learn its pricing scheme. Tearing like wildfire through the 1980s, it led to appalling miscarriages of justice like the McMartin preschool case, in which the hapless owners and employees of a daycare center in Manhattan Beach, California, were accused of being depraved Aleister Crowley-like abusers. Less nefarious is the information that skims the surface of the Dark Web, in a zone called the Deep Web. Additionally, information being sold on the Dark Web isn’t a one-time issue.